As India accelerates its digital transformation, data has become the foundation driving innovation, customer engagement, and business growth. However, with this rapid expansion comes an equally important responsibility protecting personal data.
The Digital Personal Data Protection (DPDP) Act is India’s landmark legislation that establishes a comprehensive framework for data privacy and governance. For organizations, compliance is not just about avoiding penaltiesit is about building trust, ensuring transparency, and creating a resilient data ecosystem.
Send us a message
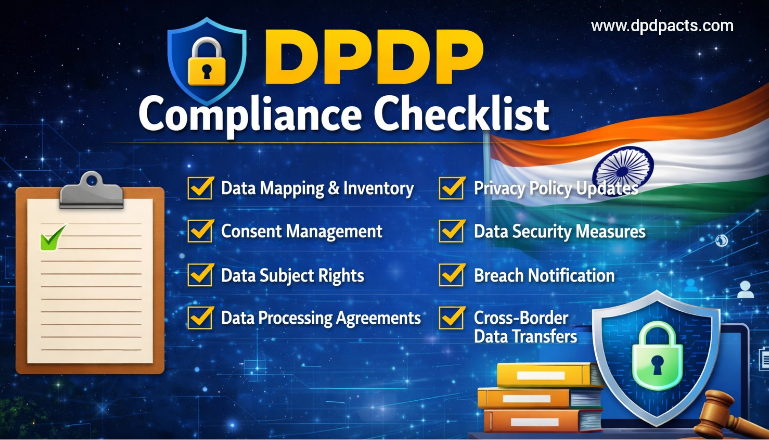
This in-depth guide expands on the DPDP compliance checklist, offering practical insights, examples, and implementation strategies to help organizations navigate compliance effectively.
Understanding the DPDP Act: A Deeper Perspective
The DPDP Act applies to:
- Businesses operating in India
- Global companies processing data of Indian residents
- Digital platforms, SaaS providers, and e-commerce companies
It introduces key roles:
- Data Principal → The individual whose data is being processed
- Data Fiduciary → The organization collecting/processing data
- Data Processor → Third-party entity processing data on behalf of fiduciary
Core principles include:
- Lawful processing
- Purpose limitation
- Data minimization
- Accuracy
- Storage limitation
- Accountability
Detailed DPDP Compliance Checklist
Let’s break each requirement into actionable and detailed steps:
- Data Mapping & Inventory (Foundation of Compliance)
What is Data Mapping?
Data mapping is the process of identifying how personal data flows through your organization—from collection to deletion.
Steps to Implement:
- Identify all data sources:
- Websites, mobile apps
- CRM systems
- HR systems
- Payment gateways
- Categorize data:
- Personal identifiers (name, phone, email)
- Financial data
- Sensitive data
- Map data flow:
- Where data is collected
- Where it is stored
- Who accesses it
- Where it is shared
- Create a Data Inventory Register:
- Data type
- Purpose
- Storage location
- Retention period
Example:
An e-commerce company collects name and address for shipping, payment information passed to a payment processor, and email for marketing campaigns. Each of these must be documented and justified.
- Consent Management (The Core of DPDP)
- What Makes Consent Valid?
Valid consent must be freely given, specific to its purpose, fully informed, and unambiguous.
Detailed Implementation:
- Use opt-in mechanisms (no pre-ticked boxes)
- Separate consent for different purposes:
- Marketing
- Analytics
- Third-party sharing
- Provide granular controls:
- Users can choose what they agree to
Consent Withdrawal:
- Add “Withdraw Consent” button in:
- Account settings
- Emails
- Mobile apps
Example:
- Instead of a single ‘I agree to terms and marketing’ checkbox, use separate opt-ins: one for terms of service and one for marketing email consent.
- Privacy Notice & Transparency
Key Elements of a Privacy Notice:
- Identity of the organization
- Purpose of data collection
- Legal basis (consent)
- Data sharing details
- User rights
- Grievance redressal contact
Best Practices:
- Use plain English (or regional language)
- Avoid legal jargon
- Use layered notices:
- Short summary + detailed version
Example:
Instead of complex paragraphs, use:
- Bullet points
- Icons
- FAQs within the notice
- Security Measures & Risk Management
What Are “Reasonable Security Safeguards”?
Technical Controls:
- Encryption (AES-256, TLS)
- Multi-Factor Authentication (MFA)
- Firewalls and intrusion detection systems
Administrative Controls:
- Security policies
- Employee training
- Incident response procedures
Access Control:
- Role-Based Access Control (RBAC)
- Least privilege principle
Data Breach Response Plan (Critical Requirement)
Steps:
- Detect breach
- Contain impact
- Assess severity
- Notify authority within 72 hours
- Inform affected users
Example:
- If a database is compromised: immediately isolate the affected server, reset all credentials, notify the Data Protection Board, and inform users of the risk to their data.
- Data Retention & Deletion
Key Principles:
- Keep data only as long as necessary
- Delete when purpose is fulfilled
Implementation Steps:
- Define retention timelines:
- Customer data → 3–5 years
- Transaction records → as per law
- Automate deletion:
- Scheduled purging
- Data anonymization as an alternative to deletion where appropriate
Secure Deletion Methods:
- Data wiping
- Cryptographic erasure
- Children’s Data Compliance
Strict Rules Under DPDP:
- Age threshold: under 18
- Mandatory parental consent
- No behavioral tracking
Implementation:
- Age verification during signup
- OTP-based parental approval
- Disable tracking cookies for minors
Unlike the traditional method, where consent taken from a parent was just an indication of a tick in a checkbox, Rule 10 of the DPDP Act ensures that consent obtained from the parents is done through a virtually mapped token with a digital trial, and it must be issued by an authorised entity such as the Digital Locker Service Provider which emphasises the credibility and signifies that the consent obtained is verifiable parental consent.
- Vendor & Third-Party Risk Management
Why It Matters:
Vendors often create hidden risks and third-party vendors can introduce data security and compliance risks if not properly managed. A vendor’s breach or non-compliance can directly expose your organisation to liability.
Steps:
- Conduct vendor risk assessments
- Sign Data Processing Agreements (DPAs)
- Ensure vendors follow:
- Security standards
- Breach notification rules
Example:
- When using a cloud provider, confirm data encryption in transit and at rest, verify the physical location of data storage, and check compliance certifications
- Governance & Accountability
Data Protection Officer (DPO)
Responsibilities:
- Monitoring ongoing compliance
- Handling user complaints and data subject requests
- Conducting internal audits
- Training staff on data protection obligations
- Liaising with the Data Protection Board of India
Internal Governance Framework:
- Data protection policies
- SOPs for data handling
- Regular compliance reviews
Phased Implementation Strategy
Phase 1: Discovery
- Conduct a gap analysis against DPDP requirements
- Identify risks and vulnerabilities
- Audit existing data systems and flows
Phase 2: Design
- Create compliance roadmap
- Draft Data Protection Policies and Privacy Notices
- Design consent management systems
Phase 3: Implementation
- Deploy compliance tools and technical controls
- Train employees on new policies and procedures
- Update vendor contracts and DPAs
Phase 4: Monitoring
- Conduct continuous compliance audits
- Update policies to reflect regulatory changes
- Track and report on compliance metrics
Real-World Example
A fintech company:
- Maps customer financial data
- Implements consent-based onboarding
- Encrypts all transactions
- Sets 5-year retention policy
- Appoints DPO
Result:
- Reduced breach risk
- Improved customer trust
- Regulatory readiness
Common Mistakes to Avoid
- Skipping or inadequately performing data mapping
- Using vague or bundled consent forms
- Over-collecting data beyond what is necessary
- Insufficient vendor due diligence and weak third-party controls
- Having no documented data breach response plan
Benefits of Strong DPDP Compliance
- Legal protection from regulatory penalties
- Increased customer trust and confidence
- Improved operational efficiency through better data governance
- Stronger overall data management practices
- Competitive advantage in a privacy-conscious market
Conclusion
DPDP compliance is not just a regulatory requirement—it’s a strategic advantage. Organizations that prioritize data protection will stand out in an increasingly privacy-conscious market.
By implementing this detailed checklist, businesses can build a secure, transparent, and future-ready data ecosystem.
Frequently Asked Questions (FAQs)
Q1. What is the main objective of the DPDP Act?
A1. To protect personal data and ensure responsible data processing.
Q2. Does DPDP apply to small businesses?
A2. Yes, if they process personal data of individuals.
Q3. What qualifies as personal data?
A3. Any data that can identify an individual directly or indirectly including name, email, phone number, location, and device identifiers which is in Digital Form
Q4. Is consent always required?
A4. Yes, except for specific legitimate uses defined by law, such as compliance with a legal obligation or performance of a function of the State.
Q5. How do organizations manage consent effectively?
A5. Through clear notices, opt-in mechanisms, and easy withdrawal options accessible at any time
Q6. What is the penalty for non-compliance?
A6. Penalties can be substantial – the Act prescribes fines of up to INR 250 crore per instance of violation, depending on the nature and severity of the breach.
Q7. How often should audits be conducted?
A7. At least annually, or more frequently for high-risk organizations and those Designated as Significant Data Fiduciaries.
Q8. Can data be stored outside India?
A8. Yes, subject to government restrictions and safeguards.
Q9. What is the role of a DPO?
A9. To ensure ongoing compliance with the DPDP Act, handle user grievances, conduct audits, train staff, and serve as the point of contact for the Data Protection Board of India.
Q10. How can companies start DPDP compliance?
A10. Begin with data mapping to understand what data you hold and why, then conduct a risk assessment and develop your compliance policies and consent mechanisms.